Without proper access control, businesses face unauthorized data access, lack of accountability, and risks in approval and operational processes.
Create and manage roles with specific permissions for different users.
Control access to modules, forms, and data based on user roles.
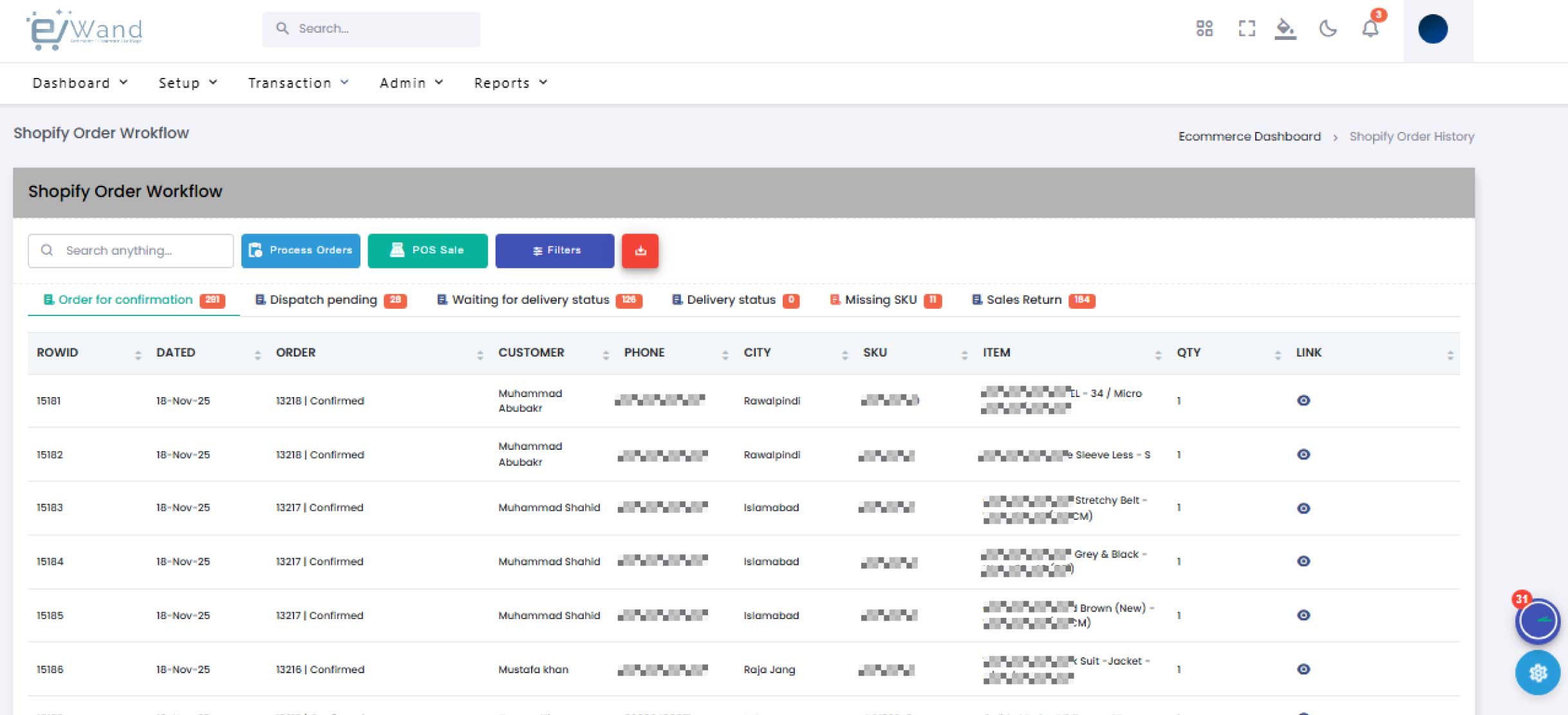
Define approval levels and workflow authorization for operations.
Track user activity and maintain logs for accountability and security.
Create roles based on job responsibilities and system access needs.
Grant access to modules, forms, and features based on roles.
Set approval workflows and authorization levels.
Track user actions and maintain audit logs for security.